Context and Objective
Large enterprises operate in increasingly complex environments, with multiple applications, internal users, third parties, and external customers. In this scenario, Identity and Access Management (IAM) is no longer just a technology—it becomes a strategic pillar for security, compliance, and operational efficiency.
CoffeeBean’s implementation services are designed to support organizations that need to structure, evolve, or sustain their IAM environments in a secure, scalable way aligned with real business needs. We provide a robust infrastructure and technical expertise to meet all client requirements, from initial assessment to continuous sustainment, ensuring security and efficiency.
IAM Challenges
Main obstacles clients face when implementing IAM solutions:
- Complex environments
- Lack of IAM planning
- Limited visibility into the current environment
- Excessive manual work
- Slow and error-prone processes
- Lack of time and team resources to focus on IAM projects
Solution
CoffeeBean offers a service designed to address these challenges, ensuring:
- A structured IAM plan
- Well-defined processes
- Workflow automation
- Alignment with major frameworks (ISO, NIST, SOX, etc.)



Pillars
The core pillars of CoffeeBean’s service are:
Assessment
Evaluation of IAM needs and definition of use cases.
Modeling
Role and group modeling, RBAC/ABAC models, policies, business rules, SoD matrix, compliance, and auditing.
Implementation
Deployment of CoffeeBean solutions.
Sustainment
Continuous monitoring to ensure requirements are met.
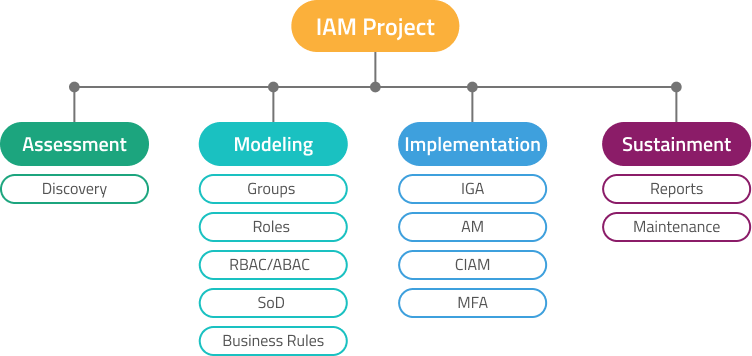
Processes are designed from assessment through sustainment, focusing on governance, compliance, and automation, aligned with standards such as LGPD, ISO 27001, SOX, and SOC.
Assessment
Assessment is the initial step, where CoffeeBean performs a specialized analysis of the environment, processes, and existing controls, identifying risks, security gaps, and improvement opportunities.
Deliverables:
- Current state assessment
- Gap identification
- Improvement roadmap
- Priority definition
- Identification of appropriate solutions
Modeling
In the Modeling phase, CoffeeBean transforms the requirements identified during the Assessment into a coherent, sustainable identity and access structure aligned with the business, serving as the foundation for IAM implementation and governance.
Deliverables:
- Group and Role Modeling: Organizational structure and application roles 3
- RBAC Matrix Modeling: Role-based modeling aligned with least privilege principles
- SoD Modeling: Access risk matrix design
- Business Rules: Workflow modeling aligned with business requirements
Implementation
Implementation is a CoffeeBean service that uses the information defined in the Modeling phase to configure the CoffeeBean platform in the client’s environment, ensuring a functional, secure IAM solution aligned with business needs.
Deliverables:
- CoffeeBean platform configured in the client environment
- Integration with defined directories and systems
- Identity policies and business rules implemented in the platform
- Solution ready for use and operational validation
Sustainment
In the Sustainment phase, CoffeeBean ensures IAM continuity and governance, enabling organizations to maintain security and compliance despite business changes, reduce operational risks, and avoid overloading internal teams.
Deliverables:
- Daily IAM flow monitoring
- Execution of access certification campaigns
- Report generation
- Maintenance of workflows and business rules
Expected Results with IAM + Service Provider
Compliance & Audit
- Specialized analysis of environment, processes, and controls.
- Compliance with LGPD, ISO 27001, SOX, SOC 1, SOC 2, and other regulations.
- Practical, prioritized recommendations for IAM evolution.
Security
- Increased security, reducing unauthorized access, data leaks, and internal risks.
- Identification of risks, security gaps, and improvement opportunities.
- Full traceability through logs and action records.
Automation & Cost Reduction
- Scalability for structured growth of identity and access environments.
- End-to-end management of processes, tools, and KPIs.
- Cost predictability and reduced reliance on internal teams.
CoffeeBean is certifying Service Provider partners.
